Every security vendor now claims artificial intelligence (AI) capabilities. Foundation models are becoming increasingly interchangeable, and the gap between what vendors promise and what programs actually deliver is widening.
The question worth asking is not which vendor has the best model. It is: what is the model running on?
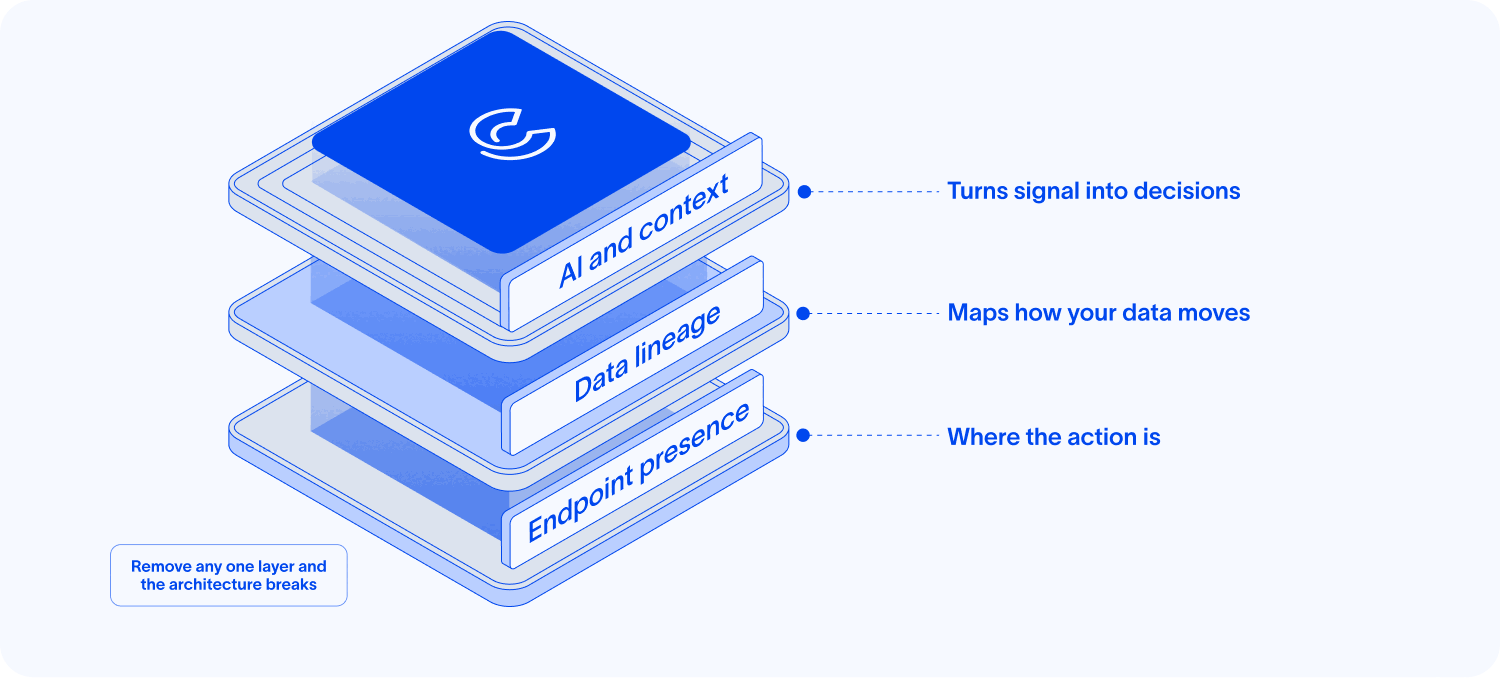
The answer to that question determines whether a data security program hardens over time or requires constant manual maintenance. And the answer has three parts: endpoint presence, data lineage, and AI that runs on the telemetry gathered from both. Each depends on the others. Miss one, and the architecture breaks.
Why the Foundation Matters More Than the Model
Data security programs fail not because of weak AI, but because of weak foundations. The model is only as useful as the data it reasons over and the visibility it draws from.
Rules-based systems have always been brittle. They work until the environment changes, a new application appears, or a user finds a workflow the rule writer did not anticipate. There are just too many exceptions to the rules. That brittleness has always been a problem. In the agentic AI era, where AI agents operate directly on endpoints, read files, store context locally, and redistribute content across applications without human oversight, the problem becomes critical.
What makes a security program adaptive is not a better algorithm applied to shallow data. It is deep, behavioral, longitudinal data built from watching how information actually moves through real organizations. That data cannot be replicated by building a new connector. It accumulates through years of presence, and that accumulation is what separates programs that get more precise over time from ones that require manual updates every time the environment shifts.
The architecture that produces that data has three elements.
Element 1: Endpoint Presence, Where the Action Is
You cannot secure what you cannot see. That principle has always been true, and the endpoint is where it is tested most directly.
The endpoint is where a developer copies proprietary code into a local AI coding tool, where an analyst pastes forecast data into an external model, where an AI agent reads files, stores context in a local window, and redistributes content across applications without a human approving each step. Every one of those events produces data. None of them are visible to tools that start and end their coverage at the cloud.
Cyberhaven Labs research shows that 49.5% of developers were using desktop-based AI coding assistants by December 2025, up from roughly 20% at the start of that year. That growth happened at the endpoint, which is exactly where cloud-first architectures have the least visibility.
The consequence is not just a gap in coverage. It is a gap in timing. Without endpoint presence, security teams are reacting to events that have already occurred. Exfiltration that has already happened, context that has already been lost, and a chain of events that is already complete. Presence is what makes real-time visibility and enforcement possible. Without it, everything else in the architecture is downstream of events the security team could not stop.
Building stable endpoint coverage at enterprise scale is genuinely difficult. Endpoint agents that provide deep visibility without degrading device performance, across OS versions and hardware configurations, are a systems engineering challenge that takes years to get right. That difficulty is also what makes the foundation durable.
Element 2: Lineage, Understanding How Your Business Works
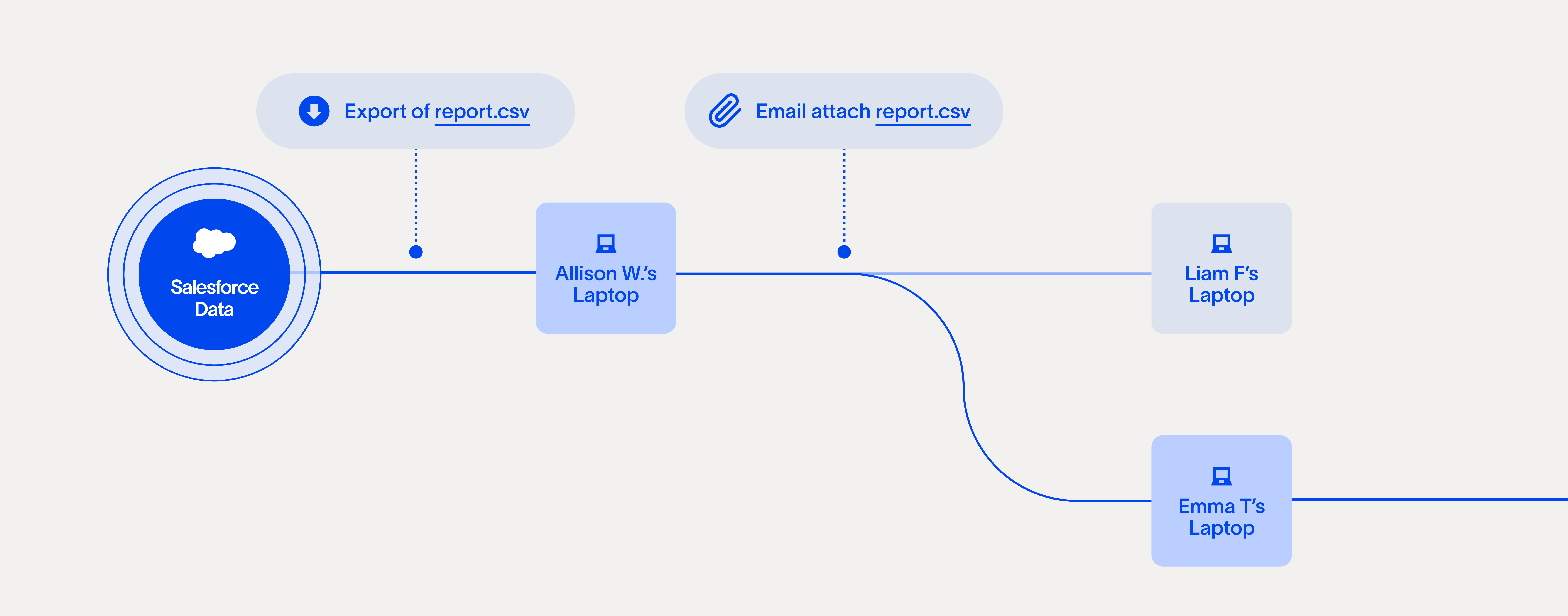
Data Lineage is the factual record of how information moves through your organization: who created it, who touched it, how it was transformed, and where it went.
Most organizations, when they build this record for the first time, discover that their data environment looks nothing like they thought it did. Lineage is not a theoretical model of how data should move. It is a mirror that reflects how data actually moves. That distinction matters enormously for security.
Risk does not live in storage. It lives in movement. A file sitting in a cloud repository is not a risk. That same file copied to a personal device, pasted into an external AI agent, and sent through personal email is a chain of events, each of which changes the meaning of what came next. A system that sees only the end of that chain cannot tell you whether the sequence was routine or a threat. A system with full lineage, from creation through every transformation to egress, can.
This is where the business specificity of a security program becomes visible. Two organizations in the same industry, running the same tools, can have entirely different data movement patterns. Effective security has to reflect those differences. Generic policies applied against a theoretical model of how data should move generate false positives. Policies grounded in observed lineage reflect the organization as it actually operates, including the workflows a rule writer would never have anticipated.
Endpoint presence is what makes lineage possible. Without the telemetry generated at the layer where data is acted upon, lineage is incomplete. You can see where data landed, but you cannot see how it got there or what happened along the way.
Element 3: AI That Turns Presence and Lineage into Decisions
Raw telemetry is noise. The volume of events generated by endpoint presence, across every application, device, and user, is not manageable by human review. The only way to turn that telemetry into actionable security decisions is through AI that understands context, and context requires lineage.
This is the dependency that makes the architecture coherent. Presence without lineage gives you data you cannot interpret. Lineage without AI gives you a history you cannot act on at scale. AI without presence and lineage gives you a model with nothing real to reason over.
The difference between generic AI applied to security data and AI trained on longitudinal behavioral data from real organizational environments shows up in three places.
- False positive volume: Generic AI models produce alerts. AI tuned on years of behavioral data from real environments can distinguish between an analyst doing something unusual and an analyst doing something risky. Those two look identical to a pattern-matching model. They look different to a model that understands the lineage and context behind each event.
- Policy that adapts: Rules reflect how security teams believe data should move. Behavioral data reflects how data actually moves. AI running on that data surfaces policy recommendations grounded in real patterns, identifies the exceptions a rule writer would not have anticipated, and hardens controls as the environment changes, rather than requiring manual updates every time a new tool appears.
- Agentic security operations: The same AI capabilities that create new risk when deployed as business tools also make security operations faster. Automated investigation, anomaly detection at machine speed, contextual triage that reduces manual review: these depend on the quality of the underlying data. An AI system running on shallow, cloud-only telemetry produces automated noise. One running on deep endpoint behavioral data with full lineage produces decisions worth acting on.
How Cyberhaven and Our Customers Put This Into Practice
The three elements are not independent features. They are a system, and the system gets more precise as it operates.
Cyberhaven and our customers have built this architecture because the alternative creates two compounding problems. Partial visibility generates false positive volume that erodes confidence in the program. And programs built on static, cloud-only views of a dynamic problem require constant manual maintenance as the environment shifts.
What the full architecture produces in practice:
- Fewer false positives, because context disambiguates signals from noise rather than treating every unusual event as equivalent.
- Policies that adapt as the environment changes, because they are grounded in observed behavior rather than rules written against a snapshot.
- Protection that follows data wherever it goes, across endpoints, cloud environments, SaaS applications, and AI tools, without requiring security teams to write new rules for every tool that appears.
- A platform that gets more precise as AI proliferates, because each new event observed adds to the lineage and improves the context the AI reasons over.
Every organization has a unique data environment. Its data movement patterns, the tools its teams use, the workflows that exist outside any official policy, are specific to how that business actually operates. Security that works has to reflect that specificity. That is what presence, lineage, and contextual AI make possible: a program that understands your organization as it actually is, not as a generic policy assumes it should be.
Data security programs that work are not built on better models applied to the same shallow data. They are built at the layer where data moves, with the context to distinguish signal from noise and the AI to act on what they see.
Explore IDC’s take on how the future of data security relies on advanced, AI-driven platforms.
Want to learn more about the value of AI-native Endpoint DLP? Watch our on-demand webinar now.


.avif)
.avif)
