Sensitive data has become the target, the signal, and the source of risk in nearly every modern security program.
Source code, customer records, intellectual property, credentials, and regulated data now move continuously across endpoints, cloud apps, SaaS platforms, browsers, collaboration tools, and GenAI applications. That movement is not inherently bad. It is how modern work gets done. But when security teams cannot see where sensitive data came from, how it changed, who touched it, where it moved, and whether that movement was risky, they are left reacting after the damage is already done.
For years, organizations have tried to solve this problem with legacy data loss prevention (DLP) tools. But traditional DLP was built for a different era. It relies heavily on static rules, pattern matching, and policy constructs that often generate more noise than clarity. Analysts are buried in alert investigations that take too long and where the response is manual. And by the time a true data exposure is identified, the data may already be outside the business.
That is the gap Cyberhaven and Torq are closing together.
Cyberhaven provides a Unified AI & Data Security Platform (DLP, DSPM, IRM, & AI Security) built on Data Lineage, tracing sensitive data across its full lifecycle: origin, movement, transformation, and destination. Torq brings AI-driven security operations, hyperautomation, case management, enrichment, and response orchestration. Together, the integration turns high-fidelity data risk signals into immediate, automated action.
Why This Matters Now
Insider risk and data loss are no longer limited to obvious exfiltration channels. Risk now shows up in everyday workflows: an engineer moving source code into a personal account, an employee uploading customer data into a GenAI tool, a privileged user syncing files to an unsanctioned destination, or sensitive data being copied, transformed, and reused in ways security teams cannot easily reconstruct.
The challenge is not just detection. It is operationalization.
Security teams need to know:
- What data was involved?
- Where did it originate?
- How did it move?
- Was the action normal or risky?
- Who owns the data?
- What business process was impacted?
- Should the response be automated, routed for approval, or escalated into a case?
Cyberhaven answers the data questions. Torq automates the operational response.
How The Integration Works
When Cyberhaven raises a data incident, that event flows into Torq with rich context, including data lineage, user behavior, asset context, and business-relevant details. Torq then enriches the event further with identity, device, HR, SaaS, and collaboration context.
From there, Torq’s automation and AI SOC capabilities can determine the right response path.
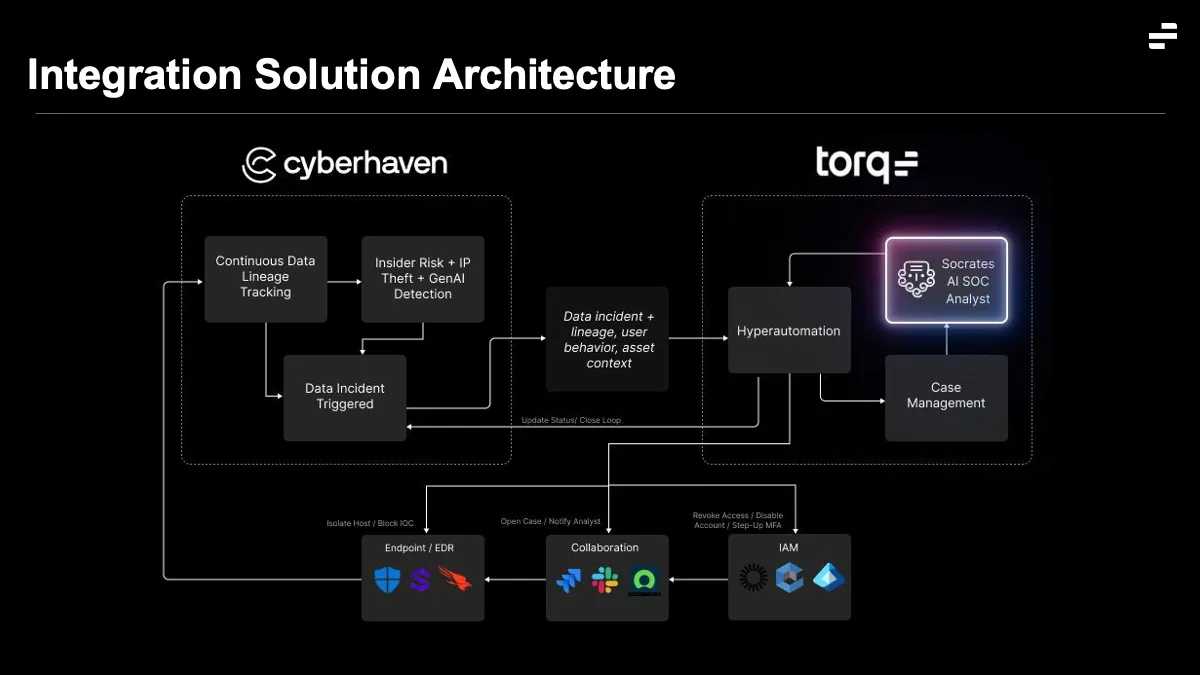
High-confidence incidents can trigger automated containment, such as blocking a risky action, disabling access through IAM, isolating a user or host through connected security tools, notifying a manager, or opening a case in the appropriate system. Ambiguous or high-impact incidents can be routed to analysts with the full timeline and context already assembled.
Once action is taken, Torq updates Cyberhaven with the incident status, creating a closed-loop remediation model where Cyberhaven remains the data security source of truth and Torq becomes the automation engine for investigation and response.
Key Customer Outcomes
The Cyberhaven and Torq integration is designed to help customers move from alert-driven data security to autonomous insider risk operations.
- Reduces analyst fatigue: Instead of manually investigating every DLP alert, analysts receive enriched incidents with the relevant data, user, asset, and business context already assembled.
- Accelerates response: Risky data movement can trigger immediate action across IAM, collaboration, case management, endpoint, SaaS, or SOC systems.
- Improves decision quality: Cyberhaven’s lineage-based context helps distinguish normal business activity from risky behavior, while Torq automates the investigative and response steps.
- Enables insider risk programs to scale without scaling headcount: The joint value proposition in the Torq slides positions the integration as end-to-end insider risk operations: Cyberhaven detects risky data movement, and Torq investigates and responds automatically.
Example use cases
1. Insider risk and IP theft response
When Cyberhaven detects sensitive data moving to a personal account, USB device, or unsanctioned destination, Torq can enrich the incident with HR, identity, user, device, and asset context. From there, Torq can block the action, notify a manager, open a case, or route the event for approval.
This turns an insider risk signal into governed action without forcing analysts to manually collect evidence across multiple systems.
2. GenAI data exposure containment
As employees adopt GenAI tools, sensitive data can flow into prompts, uploads, browser sessions, and AI-powered workflows. Cyberhaven identifies when sensitive data is being used in risky GenAI activity. Torq can then trigger the appropriate response, such as notifying the user, routing a Slack alert, escalating to a case, or applying additional containment based on policy.
3. Accelerate data incident investigation
Cyberhaven provides the full data lineage behind an incident. Torq uses that context to build the incident timeline, correlate activity across tools, surface the highest-risk events, and route the case to the right analyst or workflow. What previously required hours of manual investigation can now be reduced to seconds of assembled context.
As data continues to move across users, applications, AI tools, and business workflows, security teams need more than visibility. They need context, automation, and closed-loop response. Cyberhaven and Torq are delivering exactly that.





.avif)
.avif)
